Product name : Snagit 2020
Product Version : 20.1.0.4965
Operating System tested on: Windows 10 1909 (x64)
Vulnerability: Snagit Local Privilege Escalation through repairing msi installer package
Description :
After the Techsmith's Snagit Application is installed on Windows, an msi file is added to the “
c:\windows\installer”(hidden by default) directory. Some of the .msi files in there will auto-elevate when you run them. They do not prompt, even on non-admin which have been discovered by
@sandboxescaper . And also the msi installer package of techsmith corporation doesn't need to run by admin. So, even users can run installer file, doing file operation at higher privilege with no prompts required.
About bug,
after snagit application installed on windows, a random name *.msi file is added to "C:\windows\installer" directory. Then you can find that techsmith's installer package file in "C:\windows\installer" by using explorer.
Then,
I repair that *.msi file with "C:\windows\installer>
msiexec /fa 169a4170.msi" via low privilege account (non admin) and look at the process monitor (
procmon) to check the processes of repairing Techsmith installer package.
 |
| low privilege account(Non Admin) |
 |
| Repair Techsmith's installer package |
then, check process monitor
and I found some interested things which are msiexec is WriteFiles into the Folder "C:\ProgramData\TechSmith\Snagit 20\" and SetSecurityFile to
RegInfo.ini ,
PrinterPortFile with High privilege SYSTEM access which can be controlled by Everyone.
 |
| Everyone:(F) Full control |
Then, I used
symboliclink-testing-tools which have been created by
James Forshaw (@tiraniddo) from Project Zero to create symbolic link.
I created Hardlink to the file "C:\windows\win.ini" which doesn't have access control by low privilege user and repairing the installer package again by running "
msiexec /fa 169a4170.msi"
 |
| Access is denied by low privilege account |
Then, created hardlink to that win.ini and repaired.
 |
| Created Hardlink and repair msi |
After the repairing is finished, the file "C:\windows\win.ini" can be access controlled by Everyone.
 |
| C:\windows\win.in Everyone:(F) |
B00M !!! xD I can fully control that file.
To get SYSTEM shell with that bug, we can use "
from-arbitrary-file-overwrite-to-system" of
@decoder_it .
I modified it as simple.
FileWrite Weapon:
https://github.com/sailay1996/FileWrite2system
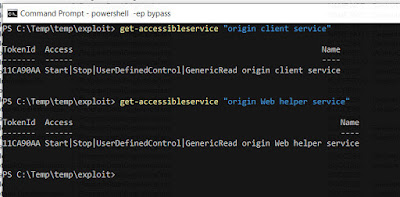
To Exploit this bug,
Create hardlink to file "
C:\Windows\System32\DriverStore\FileRepository\prnms003.inf_amd64_e4ff50d4d5f8b2aa\Amd64\PrintConfig.dll", then you can get fully control access on that dll file
PrintConfig.dll . After you get fully control , run that powershell script and you will get SYSTEM shell .
 |
| nt authority\system |
B00m !!!! You g0t SYSTEM shell.
Thanks for reading.
@404death
One click poc comming soon for this bug.
https://github.com/sailay1996